After attending Cisco Live in Vegas just two weeks ago, I returned to Las Vegas this week for HPE’s Industry Analyst Summit at HPE Discover 2024. It was HPE’s showcase to catch the AI lightning in a bottle, highlighting their ambitions and innovations in the rapidly evolving AI landscape. Below are three things that stuck out to me: HPE’s ambitious AI vision, cautious networking strategies, and the balance between Atmosphere and Discover.
HPE’s Ambition: Becoming the Enterprise AI Hardware Provider of Choice
Like many other vendors, HPE has overpivoted on AI. Labeling everything as AI dilutes genuine AI advancements. However, HPE’s effort to be the go-to enterprise hardware vendor for AI server hardware and solutions is noteworthy.
The newly announced NVIDIA AI Computing by HPE aims to accelerate the generative AI industrial revolution. This collaboration includes NVIDIA’s powerful GPUs, DGX systems, and software, combined with HPE’s advanced water-cooling from the high-performance computing world. The stack leverages NVIDIA’s Ethernet and InfiniBand solutions for internal networking. While HPE played it safe by using NVIDIA’s networking, it must sting the HPE networking folks to be sidelined in favor of NVIDIA’s components. This approach contrasts sharply with Cisco’s, where they ensured Cisco networking had a prominent role in their joint hardware stack with NVIDIA. Nonetheless, Jensen Huang, NVIDIA’s CEO, showing up at HPE Discover but not Cisco Live might signify stronger backing for HPE.
Playing It Safe in Networking Amidst Strategic Shifts
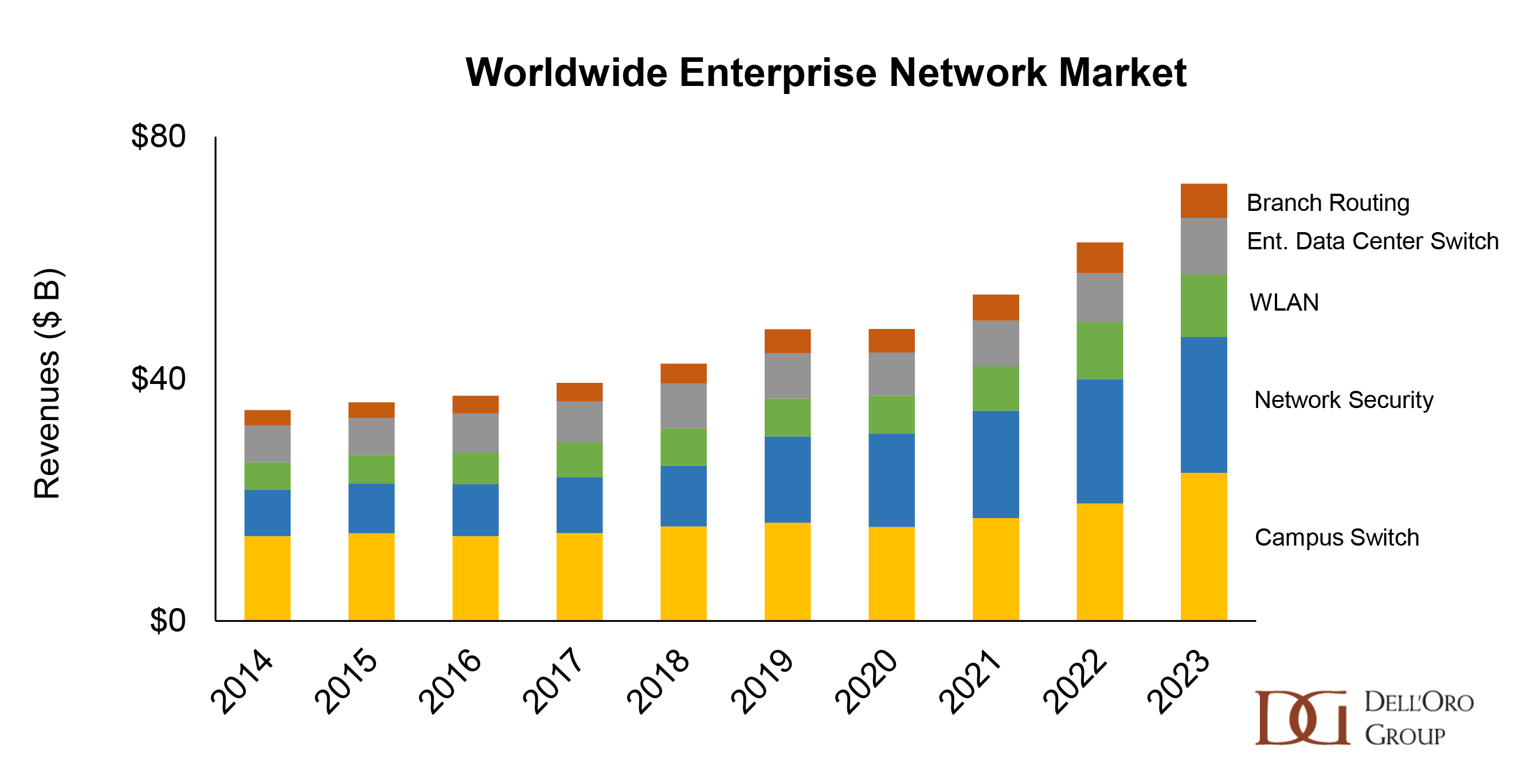
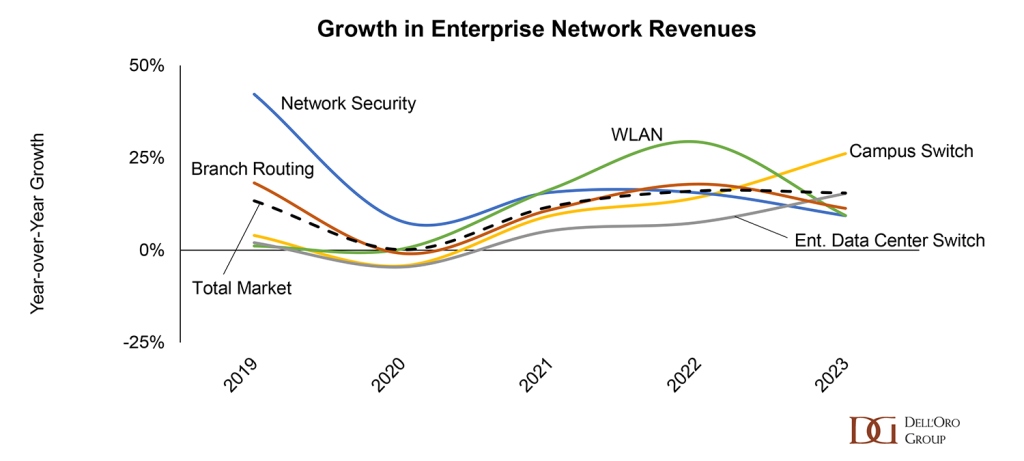
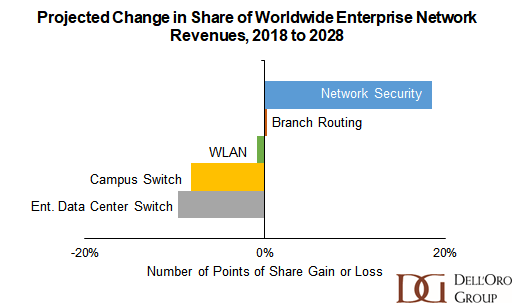
HPE Aruba Networking played it relatively safe at Discover 2024, likely influenced by the ongoing Juniper acquisition. When Juniper arrives, strategy and tactics will undoubtedly be up for grabs again. Earlier this year, I wrote a blog about what the acquisition means for HPE’s network security aspirations, and my colleague Sian Morgan wrote a great blog about how the acquisition will change the enterprise market.
Although I anticipated updates on the Juniper acquisition, the timeline remains unchanged, targeting the end of the year or early 2025. Competitors are capitalizing on this uncertainty, generating FUD to steer business away from HPE and Juniper.
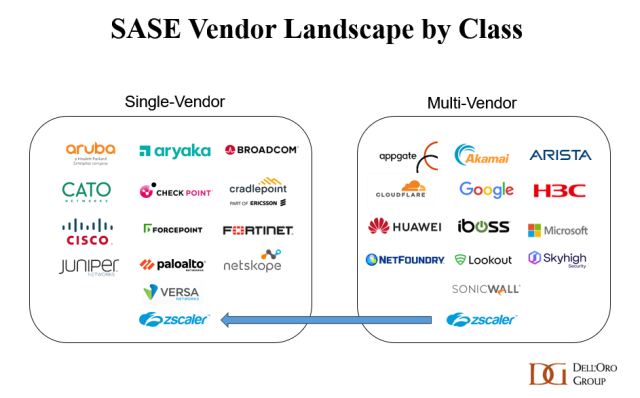
Despite no groundbreaking networking announcements, HPE Aruba showcased a broad spectrum of enhancements across its portfolio. During David Hughes’ keynote, Chief Product Officer of HPE Networking, he discussed several key advancements. A highlight was the push into “universal ZTNA” to bridge SSE’s wide-area ZTNA down into the campus with the new Aruba Local Edge. This solution identifies and enforces ZTNA on local traffic. While HPE is not the first in this area, it is far from the last; universal ZTNA is an area of active development in the industry.
Additionally, Hughes demonstrated various AI-ops demos and use cases, including AI-powered network management tools that enhance visibility, anomaly detection, and automated troubleshooting. Networking hardware also received attention with new campus switching, data center switches, SD-WAN hardware, Wi-Fi 7 access points, and even private 5G solutions. Although there were no earth-shattering networking announcements, the range of enhancements underscores that HPE Networking is not standing still or paralyzed by the ongoing acquisition of Juniper.
Balancing Atmosphere and Discover: Networking’s Place in HPE’s Vision
This year marked the first time Atmosphere, HPE Aruba’s dedicated conference, was integrated into HPE Discover. Previously, Atmosphere had a distinct identity, fostering a strong networking-focused culture. However, at HPE Discover, networking seemed to play second fiddle to the larger server and storage businesses. Many attendees lamented the loss of focus on networking and the unique culture that Atmosphere cultivated. The orange shirts of “Airheads” (Aruba’s affectionate term for its customers) were present but overshadowed by the more conservative attire of the broader HPE audience, whose only flare was a pin of HPE’s green rectangle logo.
I hope the Juniper acquisition will restore balance, bringing networking back to the forefront at future conferences. Atmosphere’s unique culture and focus should be preserved and better integrated into HPE Discover, ensuring networking and its innovations receive the attention they deserve.
Conclusion: A Glimpse into the Future
HPE Discover 2024 showcased HPE’s ambitions to lead in AI while navigating strategic shifts in networking. The partnership with NVIDIA highlights HPE’s commitment to delivering cutting-edge AI solutions, even if it means sidelining its networking components. The cautious approach in networking reflects the ongoing Juniper acquisition, with competitors eagerly watching and spreading FUD.
As HPE moves forward with the Juniper acquisition and continues to innovate, there’s hope that the unique culture of Atmosphere and the focus on networking will find a balanced place within the broader HPE and the HPE Discover show. The future promises exciting developments, and I look forward to seeing how HPE navigates these changes, driving innovation and growth in AI and networking.